Overview of DevSecOps
The practice of DevSecOps is all about implementing security in the development life cycle of an application. This minimizes the risk as well as vulnerabilities. Moreover, it brings security closer to IT and business objectives by embedding security controls and processes early in the DevOps workflow and automating the core security tasks.
The Importance of DevSecOps Today
Lately, over the last few years, the IT infrastructure underwent a huge paradigm shift, especially towards provisioning of applications dynamically and cloud computing. Adapting to these have driven benefits around agility, speed, and the overall cost of application development. Now, DevOps which defines the practices of integrating development and IT operations under a single umbrella, has facilitated frequent releases and bring more product stability at an early stage.
However, application security is just an afterthought, and, in many cases, it is identified as blocked to stay ahead in the market. Bypassing security must be considered as a high-risk strategy and that thought process needs to be changed. The DevSecOps movement is designed to facilitate this change.
Advantages of DevSecOps in the Ecosystem
Following are some of the direct benefits that one can achieve from DevSecOps:
- Early stage automation reduces the possibility of sudden glitches. This not only helps to reduce downtime or attacks but also reduces the need for security architects for manual configuration of security consoles.
- DevSecOps is a new model where everyone involved in the cycle is considered responsible for application security. So, the engineering team would not just roll out an application and leave off the responsibility of software security maintenance on the shoulder of the IT team.
- By replacing manual testing with automatic testing, organizations can mitigate the risk of a security breach. However, this transition requires the effort of setting up an organization thought process of responsibility — a practice that can stretch the benefits beyond security.
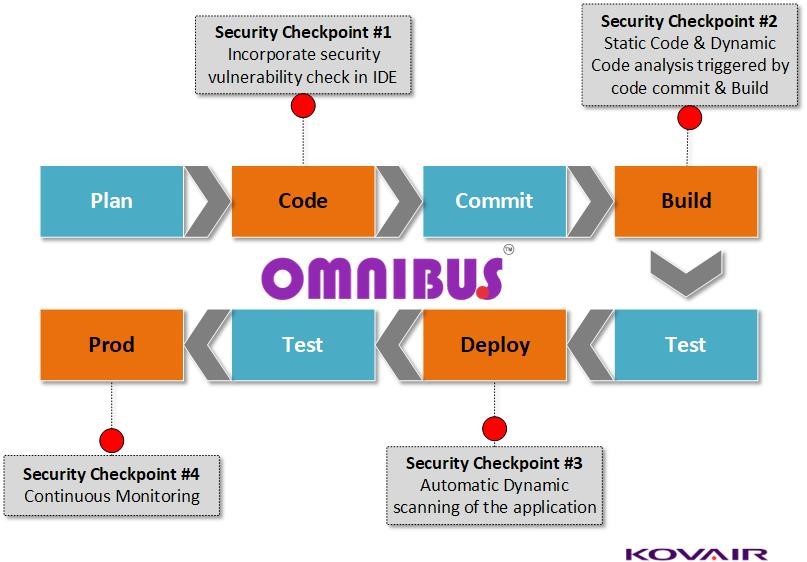
Security Checkpoints and Criteria
Integration of security into the DevOps pipeline was an integral part of the software development process. There are several security checkpoints that come into play in the DevOps pipeline. With Kovair Omnibus powered DevOps all the checkpoints mentioned below can be achieved. The data can be tracked, processed, and aggregated using Kovair reporting engine.
Integrating Security with DevOps
The task of integrating security into DevOps for delivering DevSecOps requires a new mindset, tools, and processes. To make the development process simultaneously seamless and transparent, security and risk management leaders are required to adhere to the agile and collaborative nature of DevOps. As a result of this, security becomes as seamless and silent as possible.
Stereotype security processes aren’t enough because they are often performed manually as a last step in the release of software or a product. The purpose of this latest collaborative discipline is to shape the attitude that everyone in the organization is accountable for security. This attitude lends itself to a cooperative system between business and security. Also, there are real challenges in bringing DevSecOps to life and ensuring that it delivers precise results for the business and its customers.
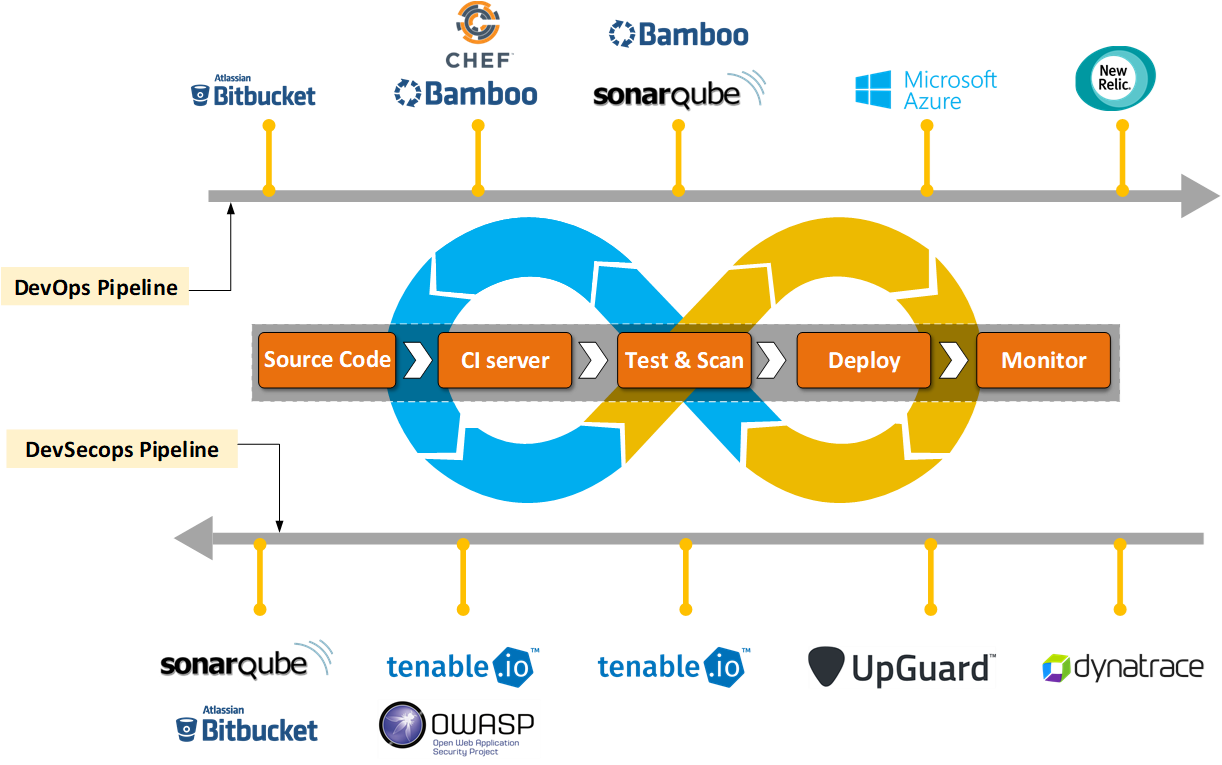
Following Pipeline Diagram explains the additional security tools which come into place when DevSecOps needs to be thought. The topmost pipeline is all about DevOps without Security and the bottom Pipeline reveals tools that can play a crucial role to incorporate DevSecOps.
Conclusion
In this new generation of business model where customer trust has become a crucial factor and the Information security forum tries to enforce companies to protect data especially the customers’ personal information, failing to deliver a secured product is not optional anymore. It can leave a negative impact on everything — from a company’s reputation to product failures.
As technology is swiftly progressing and it is our responsibility as technology experts to make sure that we too move ahead with it. Nevertheless, it is crucial that organizations implement DevSecOps gradually and actively to standardize these practices. An enduring transition, with an emphasis on the security automation aspect, will make sure that these practices suit the organization itself.
Still, organizations cannot expect to attain actual integration of development, security and operations. This can only be achieved by altering the cultural groundwork in which a discipline that places the accountability of security on everyone’s shoulder.